There and back again
It felt very similar to last year’s Disobey. This time I was a speaker and had some other duties as well, but I was still able to enjoy some very good talks and participate in the CTF competition. I left the web application hacking workshop to my colleagues (big thanks to Timo Hulkkonen especially) since I had to leave early due to personal reasons. I also missed the legendary after party, but I was more interested in learning and meeting people than partying and drinking anyway.
From hackers to hackers
Disobey is organized as a non-profit conference, which keeps the ticket prizes low. The organizers are a mix of security experts and software professionals from different companies as well as people who simply love hacking and hackers. The audience are their peers which makes it a friendly and cozy place despite the fact that there were roughly 800 people present.
As organizers are hackers themselves, they know how to make the event enjoyable for other hackers. “No suits” declared the webpage, and indeed, there were no suits and very minimal commercial advertising from the sponsors. That was very refreshing.
Disobey is a great starting point for novices as well as hardened professionals. For novices there are people who will teach things about hardware or software to get you started and people are happy to discuss things and answer questions. And if you already know many things, at Disobey you can meet other people who are very very good at what they do.
What drives the hackers?
Hackers are driven by thirst for knowledge. Not just any knowledge though, they value deep knowledge about how things work, usually only achievable by doing something. Simply reading the theory from books is not enough - only if you can successfully apply it in the real world the other hackers start taking you seriously. The name of PoC || GTFO is not a joke.
It’s not just about security vulnerabilities - it’s the overwhelming need to achieve supreme mastery of some technical topic. This same fire burns inside lock picking enthusiasts, demoscene groups and security hackers. They all make technical gadgets do something that was not intended to happen and some of it seems outright impossible, even if you see it with your own eyes. And there was plenty of that attitude and knowledge floating around the venue at Disobey.
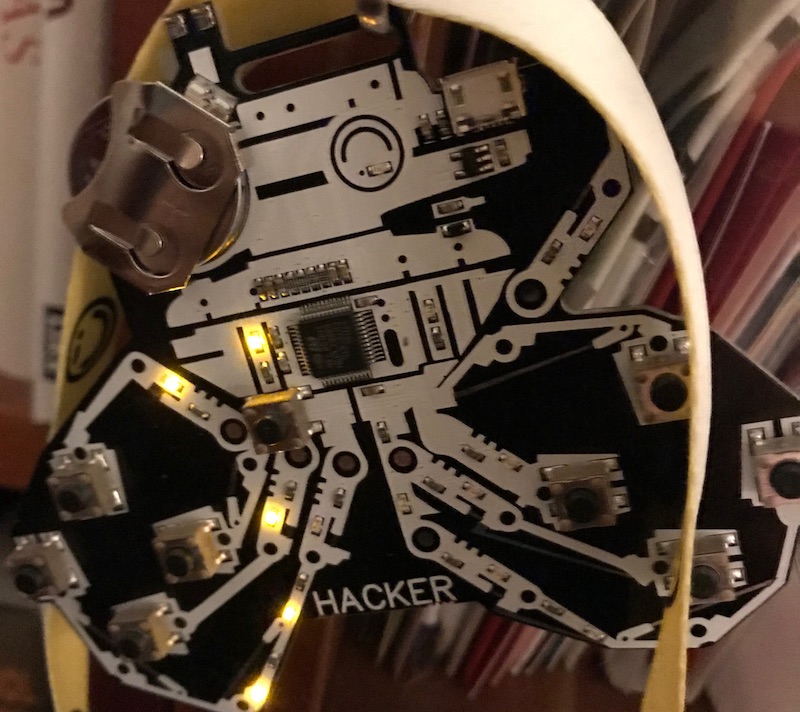
The badge is also a game controller. Something you would never see in a business oriented event.
Do you have the drive?
Do you want to truly master something? Do you seek to understand it even better than the designers of the system? That’s what you need to be successful in the field of security hacking. Many hours are spent studying, doing different tests and correcting the errors. Sometimes it doesn’t lead to any results and therefore it’s quite different from building new software and products. It took 11 months to develop a BIOS rootkit presented at the conference and less than hour to present it to others. You have to have a certain kind of mindset to get satisfaction out of that, but I was personally very impressed by k4m1’s BIOS presentation.
Serious hacking takes effort.
When I solved CTF challenges I stood up and shouted out loud spontaneously. I don’t do that in the office when I’m programming, even though I do get satisfaction and a warm feeling of accomplishment if I happen to write particularly elegant code. But that awesome feeling of “I DID IT!” is why I sometimes spend huge amount of time tinkering with something only very few people truly care about.
(If you didn’t understand what I’m talking about, you can still enjoy hacking, but security might be a difficult career choice for you.)
Until next time
Disobey has given a statement that the event will be bigger next year, but there will be limits to growth. I truly hope I’m able to attend it again as it’s my favorite even of all the demoparties, academic conferences and other gatherings I have attended. And I have attended many. People are friendly at Disobey and glad to share their knowledge and everything just works smoothly. There’s also great beer. Hard to improve that.
Awesome people from Estonia based Clarified Security won the Disobey CTF (dubbed the Finnish hacking championship) this time, but next year Team ROT will be back stronger.